The ever-evolving technology landscape and many businesses migrating to cloud platforms put huge stress on cloud security. According to security experts, implementing a shift left testing in a cloud security platform can eliminate most vulnerabilities that put enterprise systems and data at risk in the cloud environment. To make things clear, this article discusses different aspects of “Shift Left Testing” in detail.
What Is Shift Left Testing?
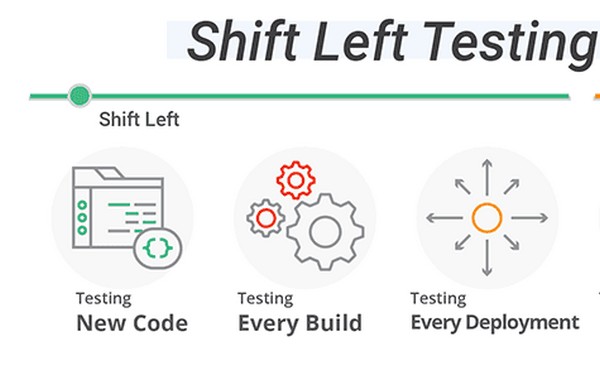
Shifting left means shifting testing as early as possible on the development axis. Shifting left practices refer to testing your security software early in the development process.
Read on: Why Azure Cloud Is Better Than Aws?
This approach offers several advantages. Enterprises can discover security flaws/defects at earlier stages where they are easier and less expensive to fix.
Why Is Shift Left Testing So Important in Cloud Security?
- Small Errors Lead to Big Problems
If you look at the cloud-scale, you will understand it is a big challenge to monitor every cloud environment element. A cloud security platform is often plagued by resources created without owners and human errors, which allow too much access after a maintenance event and misconfigurations. Misconfiguration of the cloud infrastructure is one of the main reasons for data breaches.
How Shift Left Testing Works in Strengthening Cloud Security?
Asking the security team to address misconfigurations in real-time is like asking to tilt a windmill in motion. The solution to this problem is securing baselines.
Read on: 10+ Important Things Every Security Companies Should Do
The best way to implement it is by having a contract between teams in the form of actual code. The code includes explicit and shared misinterpretations of policy. It works to establish a secure baseline through automated tools and processes employed in the software development cycle.
Establishing Universal Policy Interpretations
One of the advantages of adopting Shift Left Testing in cloud security is establishing universal policy interpretations. A baseline is a complete configuration of the application. Baselining enables all stakeholders to decide if the configuration is acceptable in the early process.
- Developers need to ensure the functions are working as intended.
- Operations need to ensure the system is efficient and reliable.
- Security teams need to know the system configuration is conformed to best security practices.
- Compliance needs to know the system can meet audit and regulatory compliance requirements.
Understanding the Know Good Design Concept
The Shift-Left Testing approach helps in defining the know good design in the early development process. It helps all parties reach an agreement in the early stages that speeds up the development process and avoids costly delays. Shift-Left Testing has also given rise to the use of the DecSecOps term, where stakeholders need to address compliance and security considerations early in the development process.
Shifting Left on Cloud Compliance
Cloud compliance refers to analyzing whether the cloud infrastructure and services are configured as per compliance requirements. Companies are required to meet different compliance standards like PCI, CIS, and GDPR. Shifting left in cloud security refers to having automation perform the analysis. This allows Development teams to have immediate access to analysis in real-time.
It also helps them know whether a specific change made in the code or the cloud infrastructure changes are running afoul in compliance. This allows development teams to course correct if needed before moving ahead.
As enterprises migrate their IT systems to the cloud environment, the question of cloud security will become more apparent. By adopting a shift left testing approach in cloud security, cloud service providers are testing their security code before merging it with their platform. This new approach allows CSPs to implement automated unit security testing of the modules that make the cloud environment more secure without sacrificing efficiency.
